.jpg)
Are you concerned about the safety of your data? BYOE (Bring Your Own Encryption) offers a secure and automated way to keep your data safe and sound. It provides users with the convenience of setting up their own encryption, allowing them to ensure control over their digital assets.
Ready to find out more? Let’s dive into what BYOE is!
Introduction to BYOE (Bring Your Own Encryption)
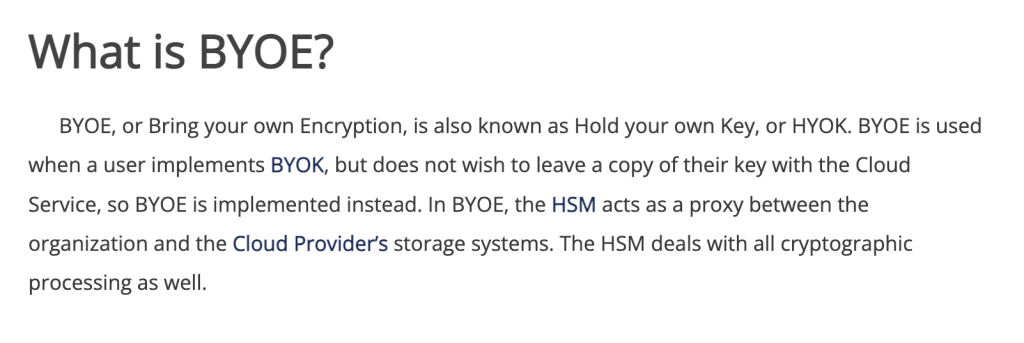
BYOE (Bring Your Own Encryption) is a cryptographic technique that allows users to have control over the encryption, key management and decryption of their sensitive data. It helps ensure that the user has the ability to protect their own data by keeping their encryption keys private. By applying BYOE in an organization, organizations can start protecting any user-generated data from unauthorized access or disclosure and reduce their risk of data loss.
BYOE uses a combination of secret sharing algorithms and client-side encryption methods to securely store data at rest with no need for an external key server. It applies cryptography as a means of protection against unauthorized or malicious activities such as root access, privilege escalation and insider privileged information theft. By using encryption to protect the data rather than depending on security measures such as firewalls, organizations can strengthen their defenses against internal or external threats while reducing their vulnerability to attack.
BYOE also provides enhanced security benefits like:
- reduced system latency due to encrypted network protocols
- granular access controls on individual files and objects
- enforcement of strictly defined policies
Moreover, because BYOE follows standards based protocols it enables rapid deployment and integrate into existing workflows making it more attractive for enterprises seeking secure collaboration over multiple locations or remote employee accesses.

Benefits of BYOE
BYOE, or Bring Your Own Encryption, is an easy way for businesses to ensure their data is secure. It allows companies to provide encryption on a per-user basis, giving users control over their own data.
One benefit of BYOE is that it enables businesses to create a secure environment where customers and employees can access sensitive information with confidence. With BYOE enabled, companies can ensure that only authorized users can gain access to the data and encryption keys used for security. This means that even if there is a breach of the corporate network, the encrypted data remains secure and unusable by unauthorized individuals.
Another major benefit of BYOE is that it makes protecting sensitive customer information much simpler and cost-effective for businesses. With the ability to control who has access to what data and encryption keys, companies no longer need to invest in comprehensive network security solutions which may not be necessary in order to protect specific data sets or employee accounts. This helps businesses save money while still ensuring sensitive customer details remain safe from malicious actors.
Finally, BYOE gives companies greater control over who can access specific customer information or areas of their networks as well as how they go about encrypting different types of data sets. Companies are able to more easily customize security settings depending on employee roles or individual user permissions while also making sure they remain compliant with any industry regulations such as GDPR or CCPA requirements when it comes to how personal customer information is secured.
Challenges of BYOE
BYOE (Bring Your Own Encryption) is a concept that provides users with the ability to control their own data security. It enables users to encrypt their data so that third-party organizations, such as internet service providers or hosting services, cannot access it. BYOE is especially beneficial for organizations that handle sensitive data, as it prevents unauthorized access of their personal or confidential information.
Due to the increasing demand for BYOE solutions, many companies have come up with a variety of different approaches and products in order to protect user data and help clients set up properly encrypted networks. However, while BYOE offers several advantages, it also presents some notable challenges; chief among these are:
- Difficulty in implementing: Many businesses may struggle with setting up and configuring BYOE solutions within their IT infrastructure because the process can be complex and require specialized expertise and resources.
- Cost of implementation: Implementing BYOE can involve significant costs due to extra hardware installation requirements or specialist software licenses for encryption purposes.
- Risk in key management: When relying solely on BYOE solutions, there’s a risk that an employee who leaves the company may still possess an encryption key for certain networks or databases; this could put corporate data at risk if this key falls into malicious hands outside of the organization’s control.
Different Types of BYOE
BYOE (bring your own encryption) is an encryption system that allows user data to be stored, shared and retrieved without a company being able to access the content. It’s a decentralized solution that allows control of data to reside with the user rather than the company hosting or controlling it.
BYOE implementations come in a few different forms and variations. Some common types include:
- Client-Side Encryption: This type of BYOE system encrypts or scrambles files on a user’s device before they are sent out or stored on another server.
- Server Encryption: In this kind of BYOE implementation, all data that is sent, stored or transmitted is encrypted on the server side, meaning users do not have to do perform any additional steps in order to receive full protection.
- Network Encryption: This system involves having an ‘encryptor’ installed on your network that provides end-to-end encryption for all communications within it. It also helps protect devices from network threats and intrusions by scrambling transmissions.
No matter which type of BYOE implementation you choose, ensure that all components are securely configured, appropriately robust key management systems are employed and trustworthy cryptographic processes are used in order to provide maximum protection for users’ digital assets.
Regulatory Compliance with BYOE
Bring Your Own Encryption (BYOE) provides organizations with the ability to ensure regulatory compliance when using cloud services or other hosted environments. With BYOE, organizations are able to take control of their encryption keys, providing another layer of security and privacy for sensitive data. Through this method, organizations gain the ability to:
- Enforce data access controls using encryption keys and policies.
- Ensure user authentication, preventing unapproved users from accessing sensitive data.
- Track who has access to what data through centralized monitoring and audit logs.
- Meet industry or regional compliance regulations while still allowing businesses to use cloud services to store and analyze their data.
For many organizations dealing with large amounts of personal or confidential information, BYOE is a key component in achieving compliance requirements and staying secure in an increasingly digital landscape. Encryption allows businesses to stay compliant while utilizing external storage solutions while also providing extra security surrounding access logs and authentication protocols.
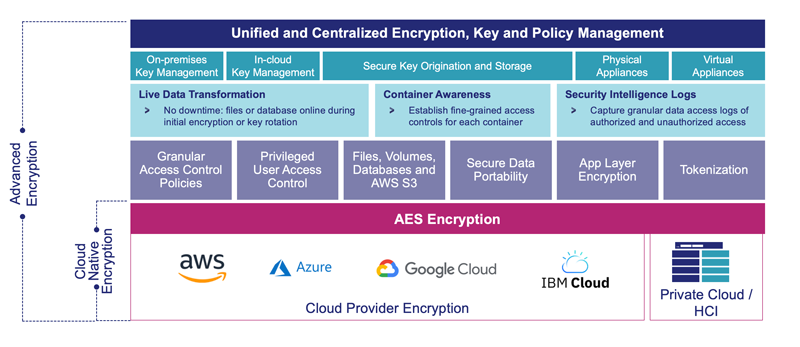
BYOE in Cloud Computing
Bring Your Own Encryption (BYOE) is a cloud computing security approach designed to give customers additional control and privacy in their cloud deployments. BYOE works by allowing users to encrypt their data prior to it being uploaded to the cloud server. This means that the encryption key is stored locally with the customer, meaning only they can access it.
By using BYOE, customers are able to prevent third parties from accessing data stored on a public cloud infrastructure without their authorization and take greater control over where they store their sensitive information. It also gives them improved compliance across multiple jurisdictions as encrypted data remains compliant even when moved across locations and boundaries.
In addition, BYOE can be extended beyond encryption alone with other security controls such as:
- Password protection
- Two-factor authentication
- System scans and pen tests
which can ensure increased security of the encrypted data in transit and at rest. This ensures that not just confidential information but all files are safe no matter who or where accesses them.
The goal of BYOE is to increase security and control for the customer, as they maintain possession of the encryption keys and have full control over access to their data.
Practical Uses of BYOE
Bring your own encryption (BYOE) is a way for organizations and individuals to use their own encryption methods and encryption keys to secure their data. With BYOE, the organization does not have to rely on third-party providers for the security of their data. This means that the organization keeps control over how its data is secured and who can access it.
BYOE offers a range of practical benefits, including:
- Greater control over encryption key management. This allows organizations to have full ownership and control over who manages their encrypted data, as well as how and when they do it.
- Improved scalability of deployment. BYOE allows organizations to quickly deploy new encryption solutions across multiple devices or applications with minimal effort or cost.
- Increased privacy protection for customers’ personal data. Organizations can take a more proactive approach to protecting customers’ personal information through encrypting sensitive information out at rest or in transit from the source system.
- Enhanced digital asset protection from cyber threats by preventing unauthorised access to any sensitive information stored in the organization’s networks.
- Reduced legal liabilities associated with data breach regulations, such as GDPR, by providing an additional layer of security for customers’ personal information.
Why BYOE Is Trending?
The BYOE philosophy provides a powerful tool for individuals and businesses looking to protect their data by ensuring that only they can access it. In the wake of increasingly frequent cyberattacks, it is more important than ever to ensure that security and privacy remain a top priority. BYOE enables organizations to take back control of their data and encryption keys, putting them at an advantage should an attacker gain unauthorized access.
Additionally, BYOE also helps organizations comply with government regulations related to data privacy and encryption. As technology continues to advance and cyber threats become increasingly sophisticated, it is essential for businesses to adopt secure practices for safeguarding sensitive information.
Thus, BYOE becomes more appealing when compared with traditional approaches to disk encryption which are less secure and require cumbersome practices in order to keep up with modern security standards.